The logistics behind cryptology in the US Military
Cryptograph.
SUMMARY
Since the dawn of communication, cryptology has been in place to help keep military secrets just that, secrets. But how it’s done ranges throughout history -- from hieroglyphics to modern-day computer code. Based on the level of technology of the time, the country itself, and even various military branches have all used unique ways to keep their messages in code.
The Roman Army used the Caesar Shift Cipher as early as the 1st century, A.D., while ancient Greece hid messages “in plain sight” by a method called stenanography. It was first seen around 440 B.C. by Herodotus. The Allies cracked the Enigma Code -- Germany’s cryptology method at the time -- to greatly shorten World War II. And in the 1970s, data encryption vastly advanced how communication was able to be hidden and protected.
In the U.S., cryptology was heavily used in each battle or wartime event. As a way of keeping information from the enemy, notes were written in code or with secret messages.
Revolutionary War Cryptology
During the U.S. bout for freedom from the British, cryptology is said to have saved many lives, even having outed Benedict Arnold before he gave up West Point to the British. Through a secret group called the Culper Spy Ring, individuals passed along messages that were obtained by spies. Membership within the organization was secret, and even the members themselves didn’t know who was all involved. The messages were then passed after being coded into the Culper Code Book, which used 763 numbers to represent various words, names and places. The book was developed by George Washington’s spymaster, Major Benjamin Tallmadge, who spied under the name of John Bolton.
Civil War Cryptology
By the time the Civil War had begun, the telegraph had been invented and was widely used as a form of communication. This allowed messages to be passed quickly among military forces. It also called in the need for code to help encrypt messages. Both Union and Confederate forces disguised their telegraph messages. Hand-written notes and vocally passed messages were also coded in order to keep communication more private.
Most notably, cryptology is known to have failed when female spies would flirt information out of soldiers. At the time, it was widely believed that women did not have a role in the war, or weren’t a valuable intelligence asset, so secrets were spilled without fear of consequence.
World War I Cryptology
During World War I, yet another technological advancement was made with the teletype cipher, which could de-code messages as they were received. This allowed messages to be sent much faster, as they did not require a person to manually translate the message. Instead they were sent live, decoded.
During the Great War, British Admiral Sir William Hall’s team famously decoded the Zimmerman Telegram. A message system between Germany and Mexico, the message stated a German plan for submarine warfare and attempting to ally with Mexico for a U.S. invasion. However, rather than spill the beans, Hall kept quiet. He knew if he outed them, they would realize the source of the information leak.
The Zimmerman was later used to decrypt more messages and eventually help win the war.
World War II Cryptology
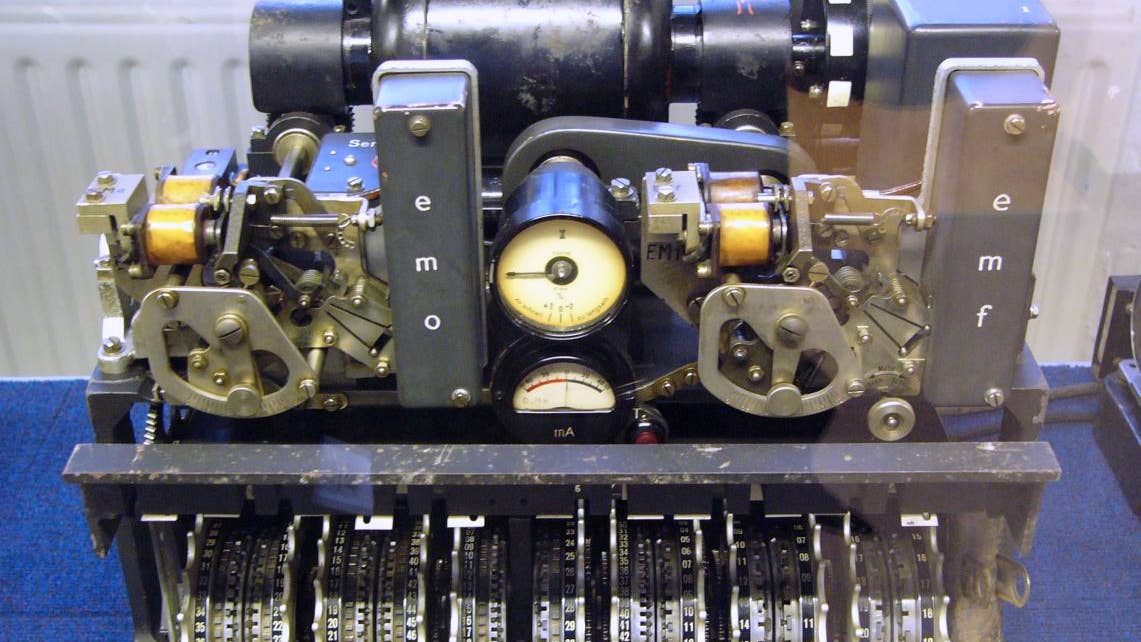
In World War II, there were entire departments dedicated to finding the meaning of hidden codes. Notably women were recruited and taught cryptology, and were sworn to secrecy about what they were doing. Their efforts, along with other countries’, soon paid off. Polish and British mathematicians decoded the Germans’ Enigma code, leading Allied forces privy to much information. The Germans soon suspected that their messages were being read, and added another rotor -- the Enigma worked by scrambling letters with these rotors -- to make messages harder to decipher.
In addition, Japanese codes were also cracked, helping bringing an end to the war.
Meanwhile, the U.S. used a machine called the SIGABA. Working similar to the Enigma, the SIGABA had 15 rotors and no reflector device, which made it harder to crack. There were no known breaches of the SIGABA through its use, up until the 1950s.
Modern day wars
With the start of Vietnam, when data became digital and could therefore be encrypted, coding messages became more complicated. And more secret. To date, there are entire departments dedicated to creating programs that keep intelligence a secret. Using binary bit sequences, security clearance levels, and countless sophisticated computer programs, and it becomes a complicated event. One that we couldn’t even guess to begin how it works … and even if we could, it’s likely that folks in suits would show up at the door. So let’s just say it’s complicated, and perhaps in several decades, we can look back and see how it was all accomplished.
SHARE