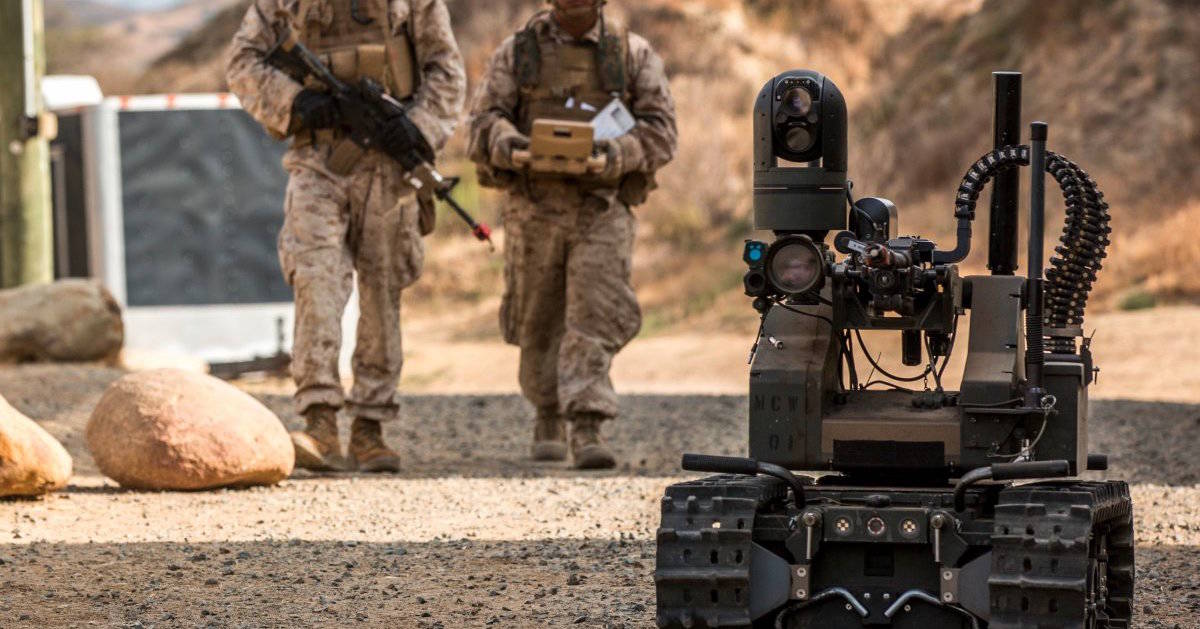
Riot police in the U.S. have long combated the challenge of containing large crowds by non-lethal means. Typically, these means are some assortment of rubber bullets, tear gas, riot shields, batons, and others. However, with the advent and rapid advancement of unmanned technology in the military—the new future of riot containment may be laser drones.

LAPD National Guard practices firing tear gas—is this soon to be a thing of the past?
That’s right—laser drones, and no, this isn’t some sci-fi renegade episode of Black Mirror or an excerpt from a long forgotten Arthur Clarke novel, this could genuinely be the next phase of riot control. The implication may seem like a scary one, but removing the human element in these situations may be a step in the right direction.
The tendency for riot situations to escalate leads the (sometimes undertrained and inexperienced) riot crews to make rash errors out of a flight or fight response. They may rely on more lethal attacks, as their non-lethal weapons could seem ineffective. However, if a robot is the one operating the non-lethal weapon, it has no regard for its own safety (and a lowered chance of human error), and it could safely utilize non-lethal means consistently, and more effectively, thus making riot situations safer for all involved.

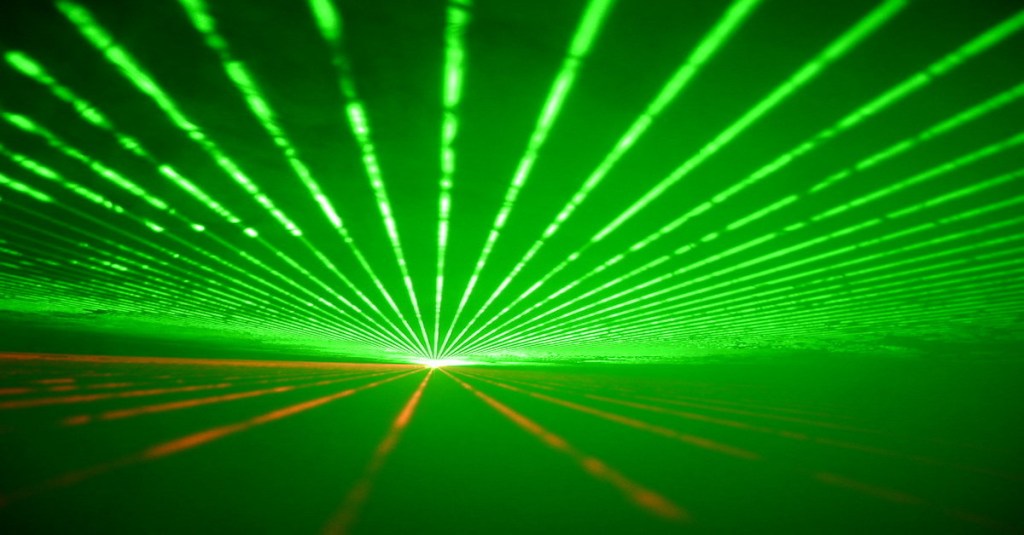
A sneaky civilian drone
Enter: the ever-popular drone. But not just any drone, a drone equipped with an incapacitating laser and a stun gun. The drone is set to make a public debut on June 25 at the International Military-Techincal Forum (aka “Army Expo”) in Moscow, Russia. The Russian Scientific and Production Association of Special Materials Corporation will be unveiling the drone.
The unmanned drone features a laser that causes temporary blindness when directed toward a crowd. This turns the drone into a flying machine dropping less-severe flashbangs, dispersing crowds without doing any long-lasting physical harm. This is also mandatory for all laser weapons created after the 1995 Protocol on Blinding Laser Weapons. The protocol dictates that laser weapons can only do permanent harm to vehicles, weapons, or sensors but not damage to humans.

U.S. Marines with Special-Purpose Marine Air-Ground Task Force Crisis Response-Africa
(1st Lt. Danielle Dixon/ USMC)
There are additional attributes that make this drone a potential game-changing riot stopper. According to Samuel Bendett, an advisor at the Center for Naval Analysis, “This drone can be a disruptor without the need to employ larger technology like crowd-control trucks and maybe even without the need to utilize soldiers or police to disperse people — that is why this UAV can also be equipped with a loudspeaker, a siren, and a thermal imager…”
This, of course, would make it the perfect vessel for domestic riots. In addition, this type of unmanned aircraft could also have use in a military sense, as it could damage enemy sensors and jam some weapons without putting boots on the ground.
As of now, the minimum safety distance for the temporary blinding laser is 13 feet. Whether or not a human could operate the drone around that distance and still be precise and efficient is yet to be seen. However, even with that limitation, the idea of a drone that could safely disperse a crowd is an interesting notion that continues to inch closer to reality.