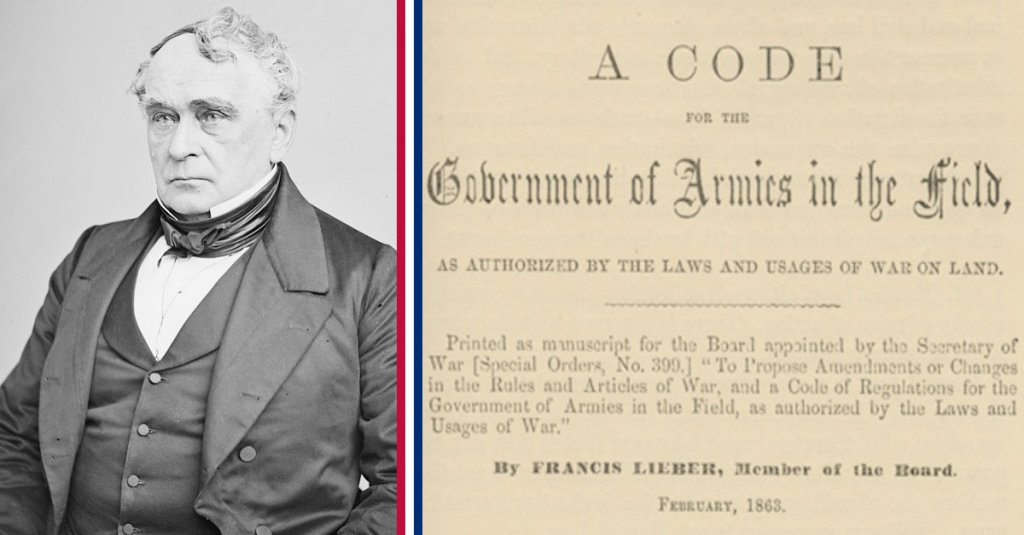
On April 24, 1863, President Lincoln issued “General Orders No. 100: Instructions for the Government of the Armies of the United States in the Field.” Commonly referred to as the “Lieber Code” after its primary author Francis (Franz) Lieber, it dictated how soldiers should conduct themselves in wartime. The main sections concerned martial law, military jurisdiction, and the treatment of spies, deserters and prisoners of war.

The Lieber Code remains the basis of most regulations for the laws of war for the United States and many other countries who used it as a template for the codification of laws of war. Before the Lieber Code, the conduct of countries and combatants was mostly based on customs, which could vary widely from country to country. The Lieber Code is the first modern attempt to codify agreed upon laws of armed conflict and humanitarian law.

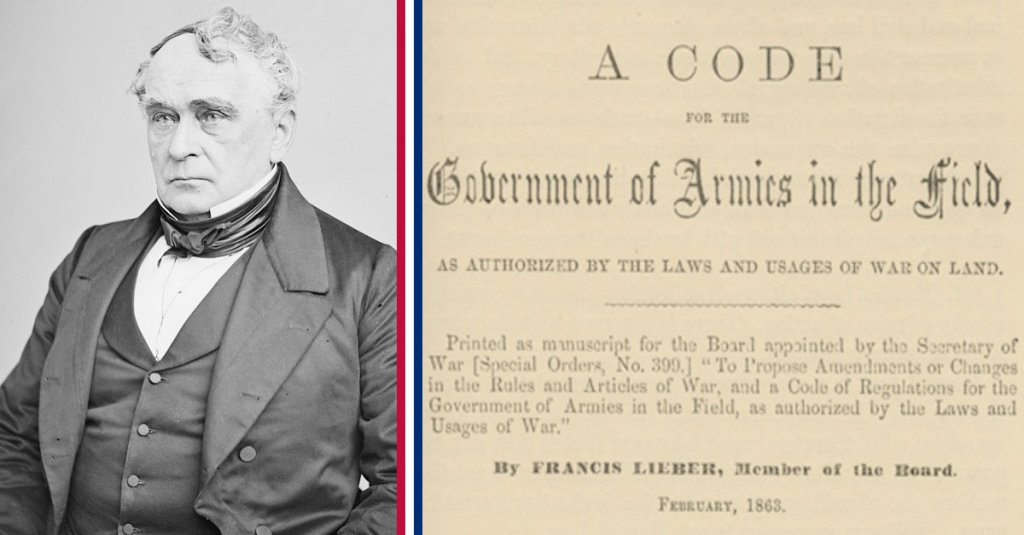
The Lieber Code was prepared by international lawyer Franz Lieber, who emigrated from Germany to the United States after being imprisoned as an “enemy of the state” due to his liberal nationalist views. In the United States, he became a professor of political science at the University of South Carolina, where he soon began to feel like an outsider due to his opposition to slavery. He moved to New York to teach at Columbia University and Columbia Law School, where he lectured on constitutional questions relating to times of war.
When the Civil War broke out in 1861, President Lincoln wanted to provide instructions to Union officers about the treatment of Confederate soldiers. He turned to Lieber for guidance about issues such as whether Confederates should be treated as traitors subject to the death penalty or as prisoners of war as well as the treatment of “fugitives” fleeing enslavement.
Lieber and a committee of four generals came together to draw up a manual to address these concerns; the instructions were endorsed by Lincoln on April 24, 1863, and distributed to all Union commanders in the field. According to historical records, the Confederate government would also adopt some of the rules in the Lieber Code as well.
