Look, if you’re not on Christmas block leave or libo or whatever your branch calls it by now, then you’re probably not going on it.
Let’s all just sit together with the funny military memes and try not to imagine what all those people with Christmas trees and matching pajamas are doing right now.
1. It’s the only dessert made up of 50 percent sadness (via Coast Guard Memes).

2. Gotta hit the ground running (via Air Force Memes Humor).

3. That yellow bird is tired of your cadence calls (via Awesome Sh*t My Drill Sergeant Said).

ALSO READ: This C-130 landing on an aircraft carrier will make you rethink physics
4. Stay low on your pushups and avoid burpees (via The Salty Soldier).

5. Dig deep, everyone (via Air Force amn/nco/snco).

6. Saving more Lincoln’s than a private box seat (via Sh-t My Recruiter Said).

7. Congrats on your restored ratings, Navy!
(via Sh-t my LPO says)

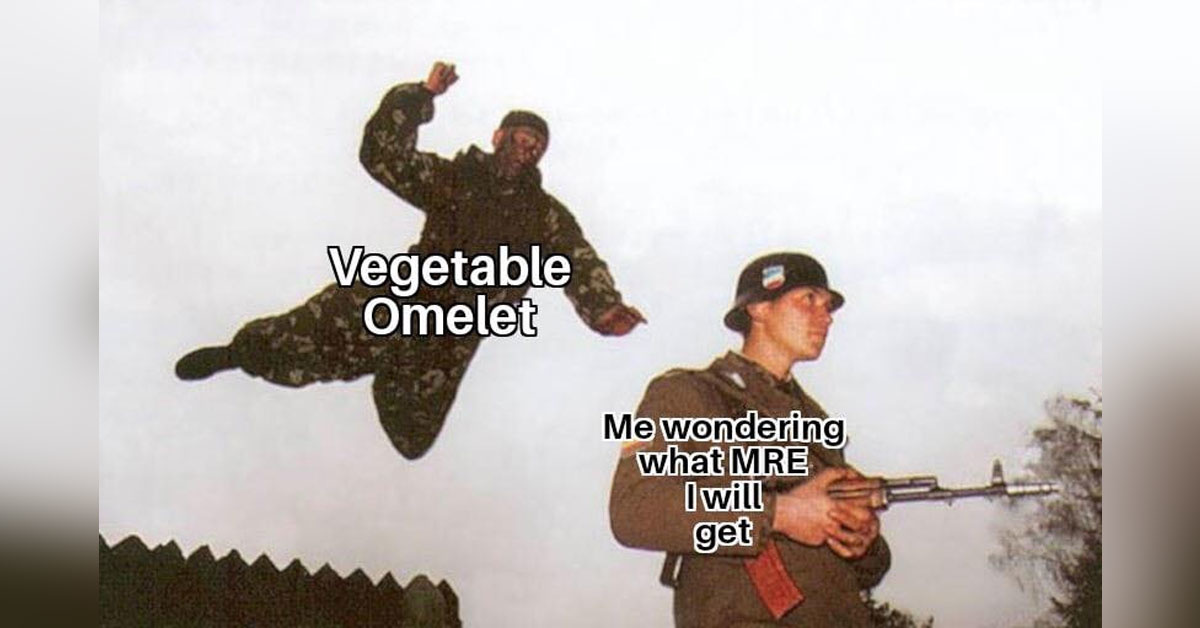
8. Don’t necessarily want to fight another nation, but it would be super nice to have clear target identification (via Pop smoke).

9. Remember to do some pushups between desserts over holiday leave (via The Salty Soldier).

10. If you think throwing up double birds when PCSing is fun, just wait till you ETS (via Lost in the Sauce).

11. When you’re not about that Rack City life (via Sh-t my LPO says).

12. In their defense, the table looks super stable (via Military World).

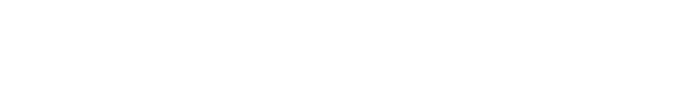
13. Oooh, how will you survive?
(via Decelerate Your Life)

Secret bonus meme 1: My Coast Guard contacts have assured me that this is brilliant (via Coast Guard Memes).

Secret bonus meme 2: Really, guys? This is literally an entire football field. Including the end zones (via Maintainer Humor).